Host Card Emulation (HCE) and Payment Tokenisation (or Tokenization for readers in America) are two highly significant new developments from 2014 that have the potential to radically change the way online and mobile payments are carried out and address some of the issues regarding security and fraud. These are not just about technology but about creating shifts in the control of payments that could impact the business models of key players.
As part of our review of the key developments in payments over 2014, I had a really interesting discussion with Sai Casula, a payments expert and Banking, Cards & Payments Consultant for Tech Mahindra. Sai shared his thoughts on Digital Payments, Tokenisation and HCE: What these mean and how they may affect the US in particular, as well as other markets world-wide. Below I share highlights from our discussions, to offer a basic introduction to these two important areas that are poised to bring about big changes in the way we pay.
Sai Casula, thanks for your time today. Please could we start with a bit of background about yourself and your organisation, Tech Mahindra?
I work for Tech Mahindra where we support customers worldwide, and in particular I am engaged in key projects with MasterCard. With the acquisition of a majority stake in Comviva in 2012, Tech Mahindra gained a strong foothold in Digital Payments space including mobile wallet, mobile POS and Cloud Payments technology. Mahindra Comviva has over 120+ deployments across 55 countries. Our mobiquity® Wallet and mobiquity® Money platform supports 2 of the top 5 Mobile Money installations globally. mobiquity® Wallet supports NFC, QR Codes, BLE and other contemporary technologies to enable mobile commerce.
 HCE is an important development going back to end-2013. Could you share a bit about what HCE is?
HCE is an important development going back to end-2013. Could you share a bit about what HCE is?
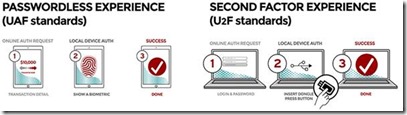
Host Card Emulation (HCE) was introduced by Google in November 2013 as part of their Android 4.4 KitKat update. It allows for cards to be issued from the cloud and used by mobile payment transactions anywhere. This was a highly significant move from Google, who had earlier faced a pushback from mobile operators in the US at the time of the launch of their Google Wallet in May 2011. It is significant because it for the first time created a level playing field for all to participate in NFC.
Prior to this it was mobile operators who could dictate terms, thanks to their control of the SIM and hence ability to own and control the Secure Element (SE) in the Universal Integrated Circuit Card (UICC) which is the smart card used in mobile phones.
With the introduction of HCE consumers with Android devices could make NFC payments using Visa or MasterCard cards provided by the consumer’s own banks. This gives banks the freedom to deploy mobile/digital payment systems everywhere.
Thanks for this background on HCE. Could you shed some light on tokenisation?
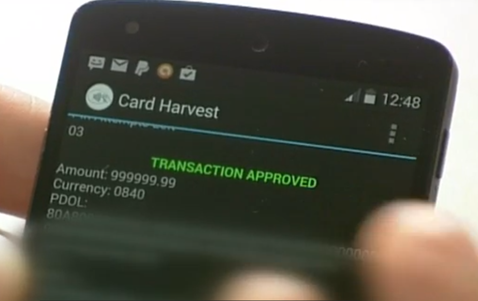
Historically there is too much fraud involved in online payments and card not present (CNP) scenarios. Consumer concerns of fraudsters stealing and using their cards online have historically inhibited people from fully enjoying online shopping.
Merchants and Card issuers in particular bear a high cost from fraud relating to payment cards. Apart from the online fraudulent transactions we also see large scale security breaches similar to Target and Neiman Marcus where the card numbers are stolen in millions and the card issuers incur an extremely high cost to replace all the cards.
Tokenisation is a model that stands to change this. Payment tokens are surrogate values that replace the Primary Account Number (PAN) with the alternate card number or “token” in the payments ecosystem. Tokens are mapped to the funding account, leveraging existing payments infrastructure and messaging formats for authorization and processing. Tokenisation reduces fraud for the entire digital payments ecosystem.
How is Tokenisation being received by the various players in the US payments ecosystem?
This brings advantages to a number of players across the ecosystem.
Firstly, the Bank Issuers really like this. When issuers provide a token to a consumer for the purpose of making a payment, this limits the use of that token to a single transaction or context, as appropriate. If there is a breach then, it is only that token that is compromised, and not the original payment card. This is also an opportunity to extend the existing card business in digital space, with more secure transactions and fewer chargebacks.
Secondly, The Networks also like this as it benefits their customers the Bank Issuers, and helps bring down the cost of fraud, within an established card scheme model.
Thirdly, any mobile wallet can accept a token, Itworks seamlessly with existing mobile payments systems and needs no changes to the Point of Sale (POS) Fourthly, merchants like this as the same token can be used on the internet as also across other channels such as mobile and POS. This brings the advantages of reduced chargebacks, faster checkout, more security and more payment options.
Last, but by no means least, consumers benefit due to better user experience and added peace of mind as they would be spared the anguish connected with a loss of a payment card or worse still the wider effects that this may have on their identity and credit history.
So there is an immediate business case and ROI for the key players through the potential reduction in fraud and the reduction of friction in Ecommerce.
What is the importance of HCE and Tokenisation in the US in particular?
Given the high-profile breaches suffered for instance by Target, Home Depot and Neiman Marcus in 2014, merchants are very concerned and anxious to reduce their exposure that comes from the existing card-on-file model. That is where Tokenisation has a welcome role to play.
The implementation of Apple Pay is an interesting case of HCE principles and Tokenisation that come together to create a seamless payments experience.
How is all this likely to affect the adoption of NFC in the US over 2015?
NFC has had a good ride recently. After a slow and unsteady history over the last 10 years, Apple Pay has created a resurgent interest in NFC. The strong user experience with Apple Pay has also increased the adoption rate of Mobile Wallets in the US Market.
Of course, NFC has a number of uses beyond payments. For instance Apple’s new iOS 8.0 is geared to health care applications.
I think the biggest war in 2015 is going to be the tokenisation war.
The big questions are who will own the key positions in the newly developing value chain? Who will manage tokens? Who will issue them? So apart from the payment networks such as Visa and MasterCard, there are many more players lined up for this. The Clearing House – Secure Token Exchange, Mahindra Comviva, Gemalto, FIS, Fiserv and First Data are all keenly interested.
At Tech Mahindra we feel uniquely position to provide an “End-to-End Cloud Payments Solution” including Cloud Payment HCE/Module, Tokenization and Mobile Application Module. We believe that our expertise in Mobile Cloud Payments, out of the box solutions and Integration expertise can help Bank Issuers bring enhanced digital experience to their customers in short time span.
So all in all we agree this is a very important space to watch then! Thanks so much for sharing your very interesting thoughts with us and I wish you every success in the key projects you are managing this year.
|
Sai Casula is VP and Banking, Cards & Payments Consultant for Tech Mahindra, and is currently based in the Greater New York City Area. Through years of experience in the banking, cards and payments industries, Sai has acquired a deep understanding across these connected areas, with strategic and operational working experience across several regions worldwide. |
Charmaine Oak is Author of The Digital Money Game and co-author of Virtual Currencies – From Secrecy to Safety
 Shift Thought is a UK-based consultancy that offers subscriptions to a unique, constantly updated portal that covers a set of 32-key services we include under Digital Money.
Shift Thought is a UK-based consultancy that offers subscriptions to a unique, constantly updated portal that covers a set of 32-key services we include under Digital Money.
To commemorate Chinese New Year 2015 we have just released “Digital Money in China 2015”, a 380 page report that completely dissects the progress of money going digital in China, and the shadow this could cast on your plans, wherever you may be in the world today.
Contact us today at contact@shiftthought.com for details on our unique resources that you can leverage to stay ahead of competition in this important, fast moving industry.
Copyright © of Shift Thought Ltd. All rights reserved. Reproduction by any method is strictly prohibited